Blog & News

Security
How to Get My Information Off the Dark Web
The dark web isn’t indexed by search engines like Google Search or Bing, but it’s where stolen data often ends up. Most exposures happen through breaches, phishing, or malware. Once your data is there it spreads quickly and is rarely removed. So, if you’re searching for how to remove your information from the dark web, the real question is what’s actually possible, and how to reduce your risk. This guide focuses on exactly that.

Anthon Wansland
CMO & Founder

Security
How to Protect Your Digital Footprint – 10 easy ways
Your digital footprint is always growing. Every search, click, post, and sign-up leaves data behind. Some of it is visible. Much of it is not.

Anthon Wansland
CMO & Founder

Insights
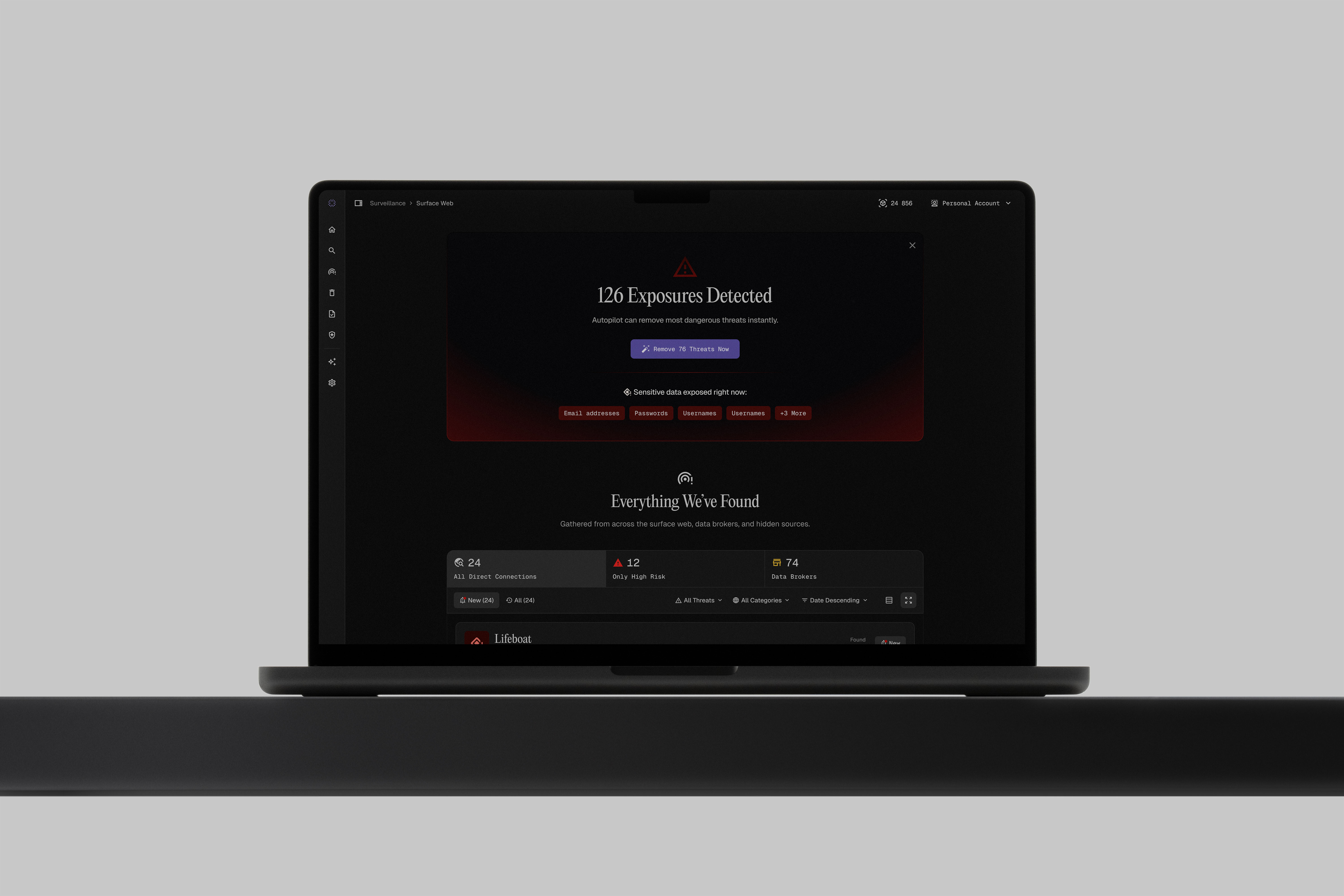
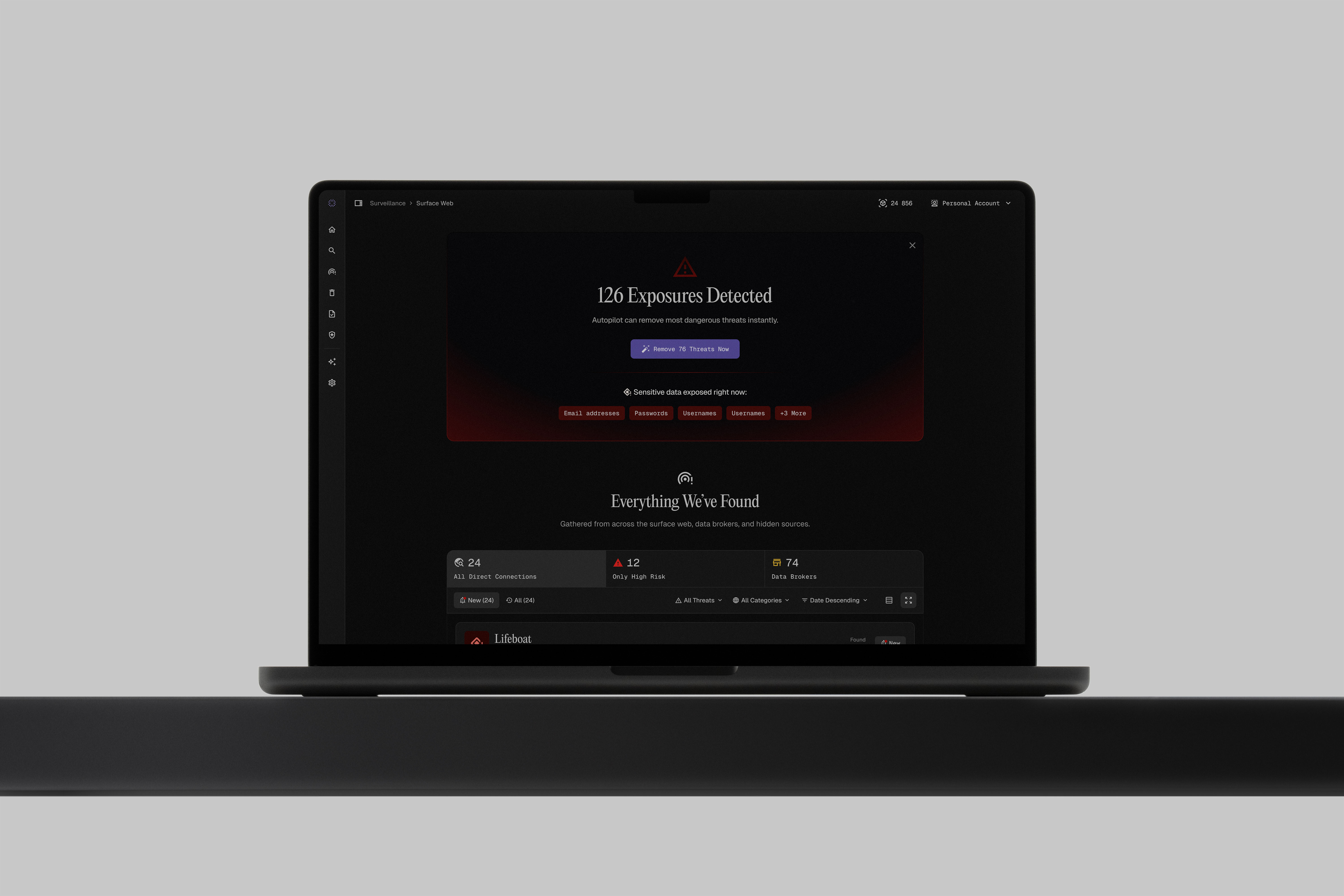
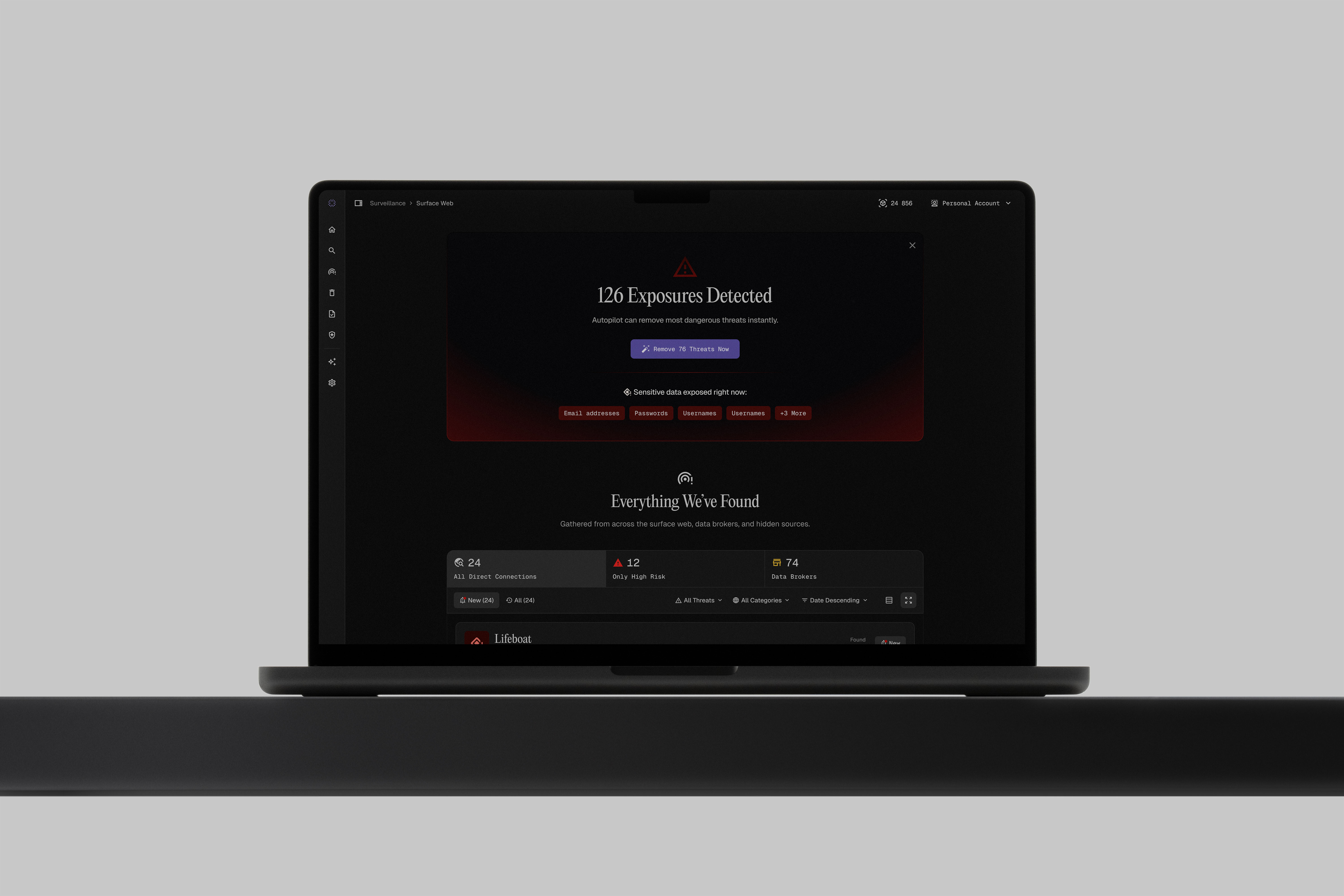
Using Autopilot
Serus Autopilot continuously scans data broker sites and automatically submits removal requests on your behalf, saving hours of manual work. Most users see significant reductions in their data broker footprint within 30-60 days, with ongoing monitoring to catch new listings as they appear.

Ida Nilsson
Customer Success Manager

Security
How to Know if Your Phone Is Hacked – 10 Signs
How to know if your phone is hacked starts with understanding what has changed. A compromised phone does not always make itself obvious. The first signs are often subtle: unusual battery drain, unfamiliar apps, strange pop-ups, or account activity that does not look right. In this guide, we explain the warning signs to look for, what they may mean, and what to do if you think your phone has been hacked.

Anthon Wansland
CMO & Founder
Security
Understand the different types of exposure
Not all online exposure is created equal. Your personal information typically appears in three ways: professional exposure (LinkedIn, company sites), social exposure (Facebook, Instagram), and data broker exposure (Whitepages, Spokeo)—and knowing the difference helps you prioritize what to tackle first.

Anthon Wansland
CMO & Founder

Security
How to Protect Yourself and Your Data from Internet Hackers
Your data is your most valuable digital asset. Protecting it doesn’t require panic. It requires clarity. Most breaches don’t come from advanced attacks. They come from small oversights. Gaps that are easy to miss, but just as easy to close. This guide shows you how to protect yourself and your data from hackers on the web.

Anthon Wansland
CMO & Founder

Insights
How to remove search results about you from Google
Removing search results starts with contacting the website owner to delete content at the source, then using Google's Remove Outdated Content tool to speed up delisting. For stubborn results that don't violate Google's policies, SEO strategies can push unwanted content down in rankings where it's less visible.

Ida Nilsson
Customer Success Manager

Security
How to Get My Information Off the Dark Web
The dark web isn’t indexed by search engines like Google Search or Bing, but it’s where stolen data often ends up. Most exposures happen through breaches, phishing, or malware. Once your data is there it spreads quickly and is rarely removed. So, if you’re searching for how to remove your information from the dark web, the real question is what’s actually possible, and how to reduce your risk. This guide focuses on exactly that.

Anthon Wansland
CMO & Founder

Security
How to Know if Your Phone Is Hacked – 10 Signs
How to know if your phone is hacked starts with understanding what has changed. A compromised phone does not always make itself obvious. The first signs are often subtle: unusual battery drain, unfamiliar apps, strange pop-ups, or account activity that does not look right. In this guide, we explain the warning signs to look for, what they may mean, and what to do if you think your phone has been hacked.

Anthon Wansland
CMO & Founder

Security
How to Protect Yourself and Your Data from Internet Hackers
Your data is your most valuable digital asset. Protecting it doesn’t require panic. It requires clarity. Most breaches don’t come from advanced attacks. They come from small oversights. Gaps that are easy to miss, but just as easy to close. This guide shows you how to protect yourself and your data from hackers on the web.

Anthon Wansland
CMO & Founder

Security
How to Protect Your Digital Footprint – 10 easy ways
Your digital footprint is always growing. Every search, click, post, and sign-up leaves data behind. Some of it is visible. Much of it is not.

Anthon Wansland
CMO & Founder
Security
Understand the different types of exposure
Not all online exposure is created equal. Your personal information typically appears in three ways: professional exposure (LinkedIn, company sites), social exposure (Facebook, Instagram), and data broker exposure (Whitepages, Spokeo)—and knowing the difference helps you prioritize what to tackle first.

Anthon Wansland
CMO & Founder

Insights
How to remove search results about you from Google
Removing search results starts with contacting the website owner to delete content at the source, then using Google's Remove Outdated Content tool to speed up delisting. For stubborn results that don't violate Google's policies, SEO strategies can push unwanted content down in rankings where it's less visible.

Ida Nilsson
Customer Success Manager

Insights
Using Autopilot
Serus Autopilot continuously scans data broker sites and automatically submits removal requests on your behalf, saving hours of manual work. Most users see significant reductions in their data broker footprint within 30-60 days, with ongoing monitoring to catch new listings as they appear.

Ida Nilsson
Customer Success Manager

Security
How to Get My Information Off the Dark Web
The dark web isn’t indexed by search engines like Google Search or Bing, but it’s where stolen data often ends up. Most exposures happen through breaches, phishing, or malware. Once your data is there it spreads quickly and is rarely removed. So, if you’re searching for how to remove your information from the dark web, the real question is what’s actually possible, and how to reduce your risk. This guide focuses on exactly that.

Anthon Wansland
CMO & Founder

Security
How to Protect Yourself and Your Data from Internet Hackers
Your data is your most valuable digital asset. Protecting it doesn’t require panic. It requires clarity. Most breaches don’t come from advanced attacks. They come from small oversights. Gaps that are easy to miss, but just as easy to close. This guide shows you how to protect yourself and your data from hackers on the web.

Anthon Wansland
CMO & Founder
Security
Understand the different types of exposure
Not all online exposure is created equal. Your personal information typically appears in three ways: professional exposure (LinkedIn, company sites), social exposure (Facebook, Instagram), and data broker exposure (Whitepages, Spokeo)—and knowing the difference helps you prioritize what to tackle first.

Anthon Wansland
CMO & Founder

Insights
Using Autopilot
Serus Autopilot continuously scans data broker sites and automatically submits removal requests on your behalf, saving hours of manual work. Most users see significant reductions in their data broker footprint within 30-60 days, with ongoing monitoring to catch new listings as they appear.

Ida Nilsson
Customer Success Manager

Security
How to Know if Your Phone Is Hacked – 10 Signs
How to know if your phone is hacked starts with understanding what has changed. A compromised phone does not always make itself obvious. The first signs are often subtle: unusual battery drain, unfamiliar apps, strange pop-ups, or account activity that does not look right. In this guide, we explain the warning signs to look for, what they may mean, and what to do if you think your phone has been hacked.

Anthon Wansland
CMO & Founder

Security
How to Protect Your Digital Footprint – 10 easy ways
Your digital footprint is always growing. Every search, click, post, and sign-up leaves data behind. Some of it is visible. Much of it is not.

Anthon Wansland
CMO & Founder

Insights
How to remove search results about you from Google
Removing search results starts with contacting the website owner to delete content at the source, then using Google's Remove Outdated Content tool to speed up delisting. For stubborn results that don't violate Google's policies, SEO strategies can push unwanted content down in rankings where it's less visible.

Ida Nilsson
Customer Success Manager
Serus by ANON AI Labs, Inc.
© 2026 Serus. All rights reserved.
Serus by ANON AI Labs, Inc.
© 2026 Serus. All rights reserved.





